You must read our article that Google and some other smartphone makers are now pushing one of the biggest updated to their Android phones in order to tackle with the Stagefright vulnerability. But you can now check if your Android device is attacked by the bug or not by installing the simple app in your phone.
Just to remind that Stagefright is a critical Android vulnerability. It allows hackers to get system or media privileges of your device when your device is processing an MMS, without need of any end-user action. To make matters worse, MMS can delete itself before you open it. With such potential, Stagefright can wreak havoc on carriers and enterprises using Android devices for business.
Gizmodo reported that this app is developed by the same team who have discovered the Stagefright vulnerability in Android. Zimperium zLabs expert and VP of Platform Research and Exploitation, Joshua Drake discovered this vulnerability and also provided patches to Google to secure Android. They also had provided these patches to carriers and vendors through Zimperium Handset Alliance.
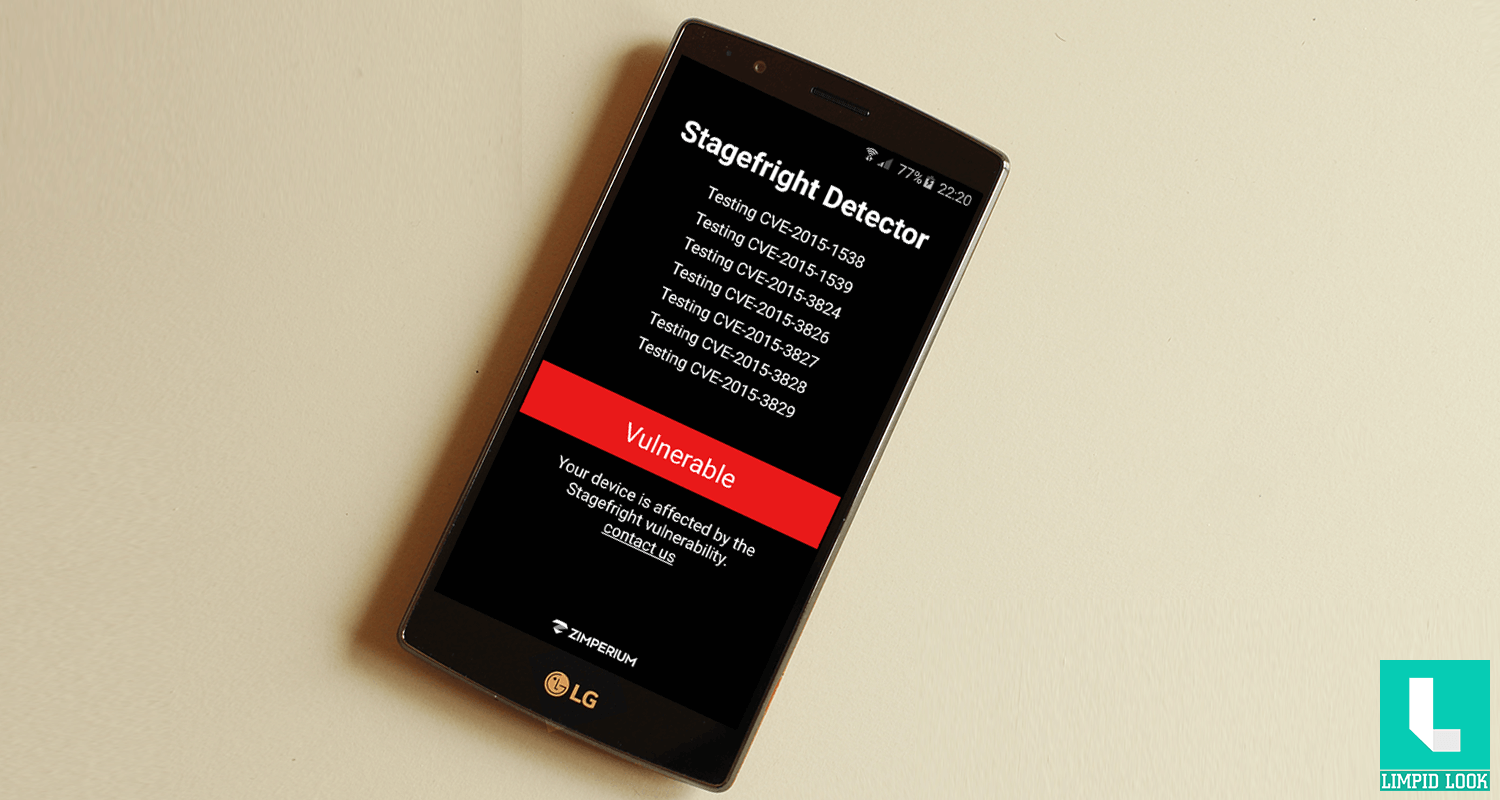
In order to test if your device is vulnerable, Zimperium built the ‘Stagefright Scanner’ app. This app will tell you two major things:
- whether your device is vulnerable
- whether you need to update your mobile Operating System
While Google has already created a fix—with some fanfare—currently only Nexus devices have been updated. If you use any other Android device, even a brand new one, you’re likely still at risk. You can use the Stagefright Detector App to find out.
You can download the Stagefright Detector app here




Add comment